Agentic AI Applications go beyond simple question-and-answer interactions. They autonomously pursue complex goals, reasoning, planning, and executing multi-step tasks with minimal human intervention. Unlike LLMs/chatbots that wait for explicit instructions, agentic systems decompose objectives into subtasks, invoke external tools (APIs, databases, code execution), and adapt dynamically.
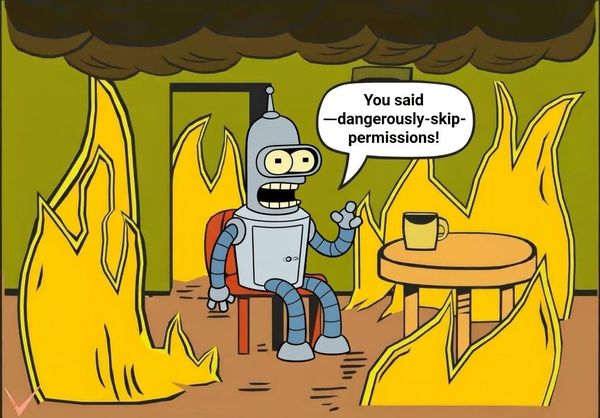
This autonomy is